Inside the Multimillion-Dollar Plan to Make Mobile Voting Happen
The bustling atmosphere of an annual conference on voting technology in Washington, DC, was the last place Joe Kiniry, a distinguished security expert specializing in elections, expected to encounter a proposition that would reshape a significant part of his professional life. Amidst discussions on electoral integrity and technological advancements, a woman approached him with an intriguing, yet somewhat unsettling, offer. She revealed she represented an affluent client whose singular interest lay in funding voting systems designed to dramatically boost voter participation. Her direct question to Kiniry was simple: did he have any viable ideas? Kiniry’s immediate, cautionary response echoed years of experience and research in the field: “I told her you should stay away from internet voting, because it’s really, really hard.” His words reflected a widespread consensus among cybersecurity professionals regarding the immense complexities and inherent vulnerabilities of online electoral processes.
It was only later that Kiniry discovered the identity of the powerful figure behind the unusual inquiry: Bradley Tusk. A prominent New York City political consultant, Tusk had carved out a formidable reputation as a shrewd "fixer," famously navigating complex regulatory landscapes for burgeoning tech giants like Uber. His early investment in Uber stock had propelled him to considerable wealth, a substantial portion of which he was now eager to deploy in pursuit of a singular, ambitious goal: the widespread adoption of online voting technology. Tusk, leveraging his persuasive prowess, eventually convinced Kiniry to collaborate. For Kiniry, despite his initial reservations, the prospect of such a well-funded endeavor held an undeniable allure, at the very least promising a valuable and intensive research project into an area fraught with both peril and potential.
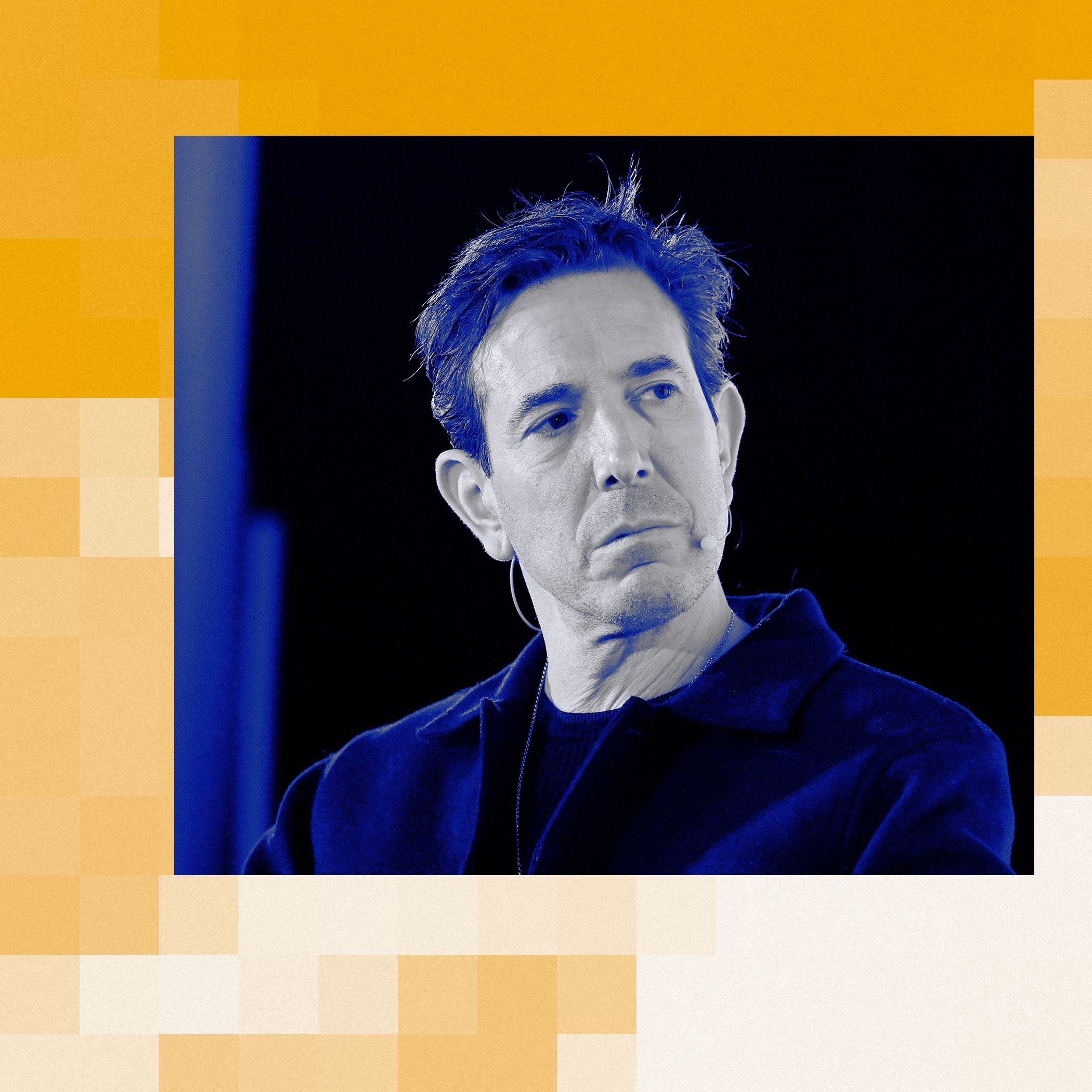
Today, Tusk proudly showcases the tangible results of that pivotal collaboration. His philanthropic venture, the Mobile Voting Foundation, is poised to unveil VoteSecure, a groundbreaking cryptography-based protocol meticulously engineered to facilitate secure ballot casting on ubiquitous mobile devices—specifically iPhones and Androids. This isn’t a proprietary, closed-source solution; VoteSecure has been deliberately developed as an open-source protocol, readily available on GitHub for global scrutiny. This transparency invites anyone—from independent researchers to rival developers—to rigorously test its resilience, propose enhancements, and build upon its foundational architecture. Already, the initiative has garnered significant traction, with two established election technology vendors committing to integrate VoteSecure, potentially enabling its deployment in actual elections as early as 2026. Tusk, with characteristic boldness, asserts that mobile voting holds the key to safeguarding and revitalizing democracy itself. However, he readily acknowledges that the true crucible of this endeavor lies not in its technical sophistication, but in the daunting challenge of securing acceptance from a skeptical public and cautious legislators—a task that he concedes will be "the really, really hard part."
Tusk’s fervent commitment to mobile voting is far from a recent whim; it represents a long-standing obsession that crystallized around 2017. It was then that he began translating his vision into concrete action, strategically funding smaller-scale elections that utilized existing, albeit rudimentary, technology to enable specific demographics, such as deployed military personnel and individuals with disabilities, to cast their votes remotely. His financial commitment to this cause has been substantial, estimated at a staggering $20 million to date, with clear intentions to continue injecting capital into the effort. When pressed on the depth of his conviction, Tusk articulates a profound disillusionment stemming from his extensive experience working with governmental bodies. This unique vantage point, he explains, has afforded him a "panoramic view" of systemic failures and inefficiencies.
Tusk firmly believes that a single, transformative "pressure point" could rectify a multitude of discrepancies between what citizens legitimately expect from their government and the often-disappointing reality they receive: significantly increased voter participation. "We get lousy, or corrupt, government because so few people vote, especially in off-year elections and primaries, where the turnout is dismal," he laments. He paints a compelling picture of a political landscape fundamentally altered by greater engagement: "If primary turnout is 37 percent instead of 9 percent, the underlying political incentives for an elected official to change—it pushes them to the middle, and they’re not rewarded for screaming and pointing fingers." For Tusk, mobile voting isn’t merely a convenience; it’s an existential imperative. We conduct our banking, manage our commerce, and exchange our most private messages via our smartphones, he argues, so why should the fundamental act of casting a ballot remain mired in analog processes? "If I don’t do it, who is going to do it?" he challenges. His rhetoric escalates further, underscoring the urgency of his mission: "If it doesn’t happen, I don’t think we’re one country in 20 years, because if you are unable to solve any single problem that matters to people, eventually they decide not to keep going."
The development journey of VoteSecure began with a critical assessment. Tusk tasked Kiniry with meticulously evaluating existing online voting platforms, including some that Tusk himself had previously financed. Kiniry’s reputation as a preeminent authority in electronic voting was a key factor. "Joe is considered the absolute expert on electronic voting," Tusk affirms. Thus, when Kiniry concluded that these existing systems were fundamentally insufficient to meet stringent security and verifiability standards, Tusk made a decisive pivot: the most effective path forward was to build a new protocol from the ground up. He subsequently contracted Kiniry’s company, Free & Fair, renowned for its expertise in secure electoral systems, to develop VoteSecure. It’s crucial to understand that VoteSecure is not a ready-to-use, "turnkey" application. Instead, it functions as the robust backend protocol, forming the secure backbone of a larger system that will still require a user-friendly interface and other operational components to become fully functional. The protocol incorporates innovative mechanisms designed to empower voters to independently verify the accuracy of their submitted ballots and to confirm that their vote has been successfully received by the election board and accurately transferred to a physical paper ballot, thereby introducing an auditable trail.
Tusk’s strategic implementation plan for VoteSecure is deliberately incremental and pragmatic. His immediate next step is to "run legislation" in a select number of cities, initiating mobile voting at the most localized levels. "Start small—city council, school board, maybe mayor," he outlines, emphasizing the need to "prove the thesis" in controlled environments. His reasoning is both humorous and practical: "The odds of Vladimir Putin hacking the Queensborough election seems pretty remote to me." This cautious approach is already bearing fruit: in the upcoming spring, certain local elections in Alaska are slated to offer mobile-phone voting as an option, utilizing software directly developed by Tusk’s foundation. Kiniry, ever the pragmatist, concurs that it is "way too soon" to consider deploying mobile voting in national elections, recognizing the immense scale and heightened scrutiny involved. However, Tusk is playing a longer game, banking on the eventual familiarity and demonstrable reliability of these systems to cultivate public trust, perhaps even surpassing the confidence currently placed in traditional paper ballots. "Once the genie’s out of the bottle, they can’t put it back, right?" he muses, drawing parallels to other transformative technologies he’s championed. "That’s been true for every tech I’ve worked on." Yet, the initial challenge remains formidable: the genie must first successfully escape the bottle, a feat that is "no cinch."
The most vehement opposition to mobile or internet voting consistently emanates from the very bastions of digital security: cryptographers and cybersecurity experts. Their collective belief is that the inherent safety risks are not merely challenging, but fundamentally insurmountable, given the current state of technology and the unique demands of electoral integrity. Consider two prominent figures who were present at that same 2017 conference alongside Kiniry. Ron Rivest, a legendary figure in computer science, famously the "R" in the groundbreaking RSA encryption protocol that underpins much of the internet’s security, a recipient of the prestigious Turing Award, and a former professor at MIT, holds an unequivocal view: mobile voting, in its current conceptualization, is "far from ready for prime time." "What you can do with mobile phones is interesting, but we’re not there yet, and I haven’t seen anything to make me think otherwise," he states firmly. Rivest criticizes Tusk’s commercially driven approach, suggesting it prioritizes real-world deployment over foundational academic rigor. "Tusk is driven by trying to make this stuff happen in the real world, which is not the right way to do it. They need to go through the process of writing a peer-reviewed paper. Putting up code doesn’t cut it."
Similarly, David Jefferson, an esteemed computer scientist and voting expert, remains largely unimpressed. While acknowledging Kiniry’s undisputed standing as one of the nation’s foremost experts in voting systems, Jefferson views Tusk’s ambitious endeavor as ultimately "doomed." He concedes the theoretical possibility of "rock-solid cryptography" within such a system but argues that this technical perfection does little to mitigate the broader, systemic insecurities inherent in online voting. "Open source and perfect cryptography do not address the most serious vulnerabilities," Jefferson asserts, hinting at issues beyond mere encryption, such as malware on voter devices, coercion, or the integrity of the overall election infrastructure.
Kiniry, naturally, offers a robust counter-argument to the critiques leveled by his peers. Regarding the call for peer-reviewed papers, he confidently states, "We’ll get to that." He argues that the extensive work involved in developing and releasing the initial version of VoteSecure, with its detailed cryptographic protocols and open-source availability, effectively provides "the community with something like the equivalent of half a dozen papers for review." Tusk, ever the pragmatist and less inclined to academic niceties, is even more dismissive of the critics. "They’ve never seen what we’ve built," he retorts, implying that their skepticism is based on preconceived notions rather than an informed evaluation of VoteSecure’s specific architecture. He contends that their "zero-tolerance approach" to any potential flaw in a new system conveniently overlooks the inconvenient truth that the current, traditional voting systems are themselves far from perfect, plagued by their own set of vulnerabilities and inefficiencies.
However, beneath the technical sparring over cryptography and peer review lies a deeper, more profound challenge that may render all arguments about the safety and verifiability of mobile voting largely moot. In the not-too-distant past, when Tusk first became captivated by the concept of digital ballot casting, conversations surrounding election safety were predominantly conducted under the rational auspices of science, mathematics, and meticulous accounting. The public, by and large, reposed a fundamental trust in their voting systems, a trust largely justified by numerous independent studies consistently demonstrating that instances of election fraud constituted only a minuscule fraction of votes cast. That bedrock of public trust, tragically, has been eroded, perhaps irreparably. In the shadow of events post-2020, instigated by "one sore loser," the entire issue of electoral integrity has become tragically "fraught with doubt and loathing."
In this highly polarized and deeply suspicious environment, introducing an unfamiliar, technologically advanced alternative like mobile voting would be akin to "introducing cordite into the process." Even if, through some extraordinary feat of engineering and transparency, a mobile system could be unequivocally verified as 100 percent secure, it would take merely a single, ill-intended charge—a baseless accusation of external hacking or systemic manipulation—to cast a shadow of suspicion over an entire election result. The devastating impact of such accusations is not merely hypothetical; one need only recall the bogus charges leveled against Dominion Voting Systems. Despite comprehensive vindication through legal processes, the company suffered such profound reputational damage that it ultimately underwent a change in ownership and a rebranding. This chilling precedent underscores a critical distinction: while "internet voting is really, really hard—but solvable" from a purely technical standpoint, the more intractable problem is an electorate that has lost its collective faith, an electorate that "won’t accept a vote count it doesn’t like," irrespective of its proven accuracy. The ultimate success or failure of Tusk’s multimillion-dollar plan may hinge less on cryptographic brilliance and more on the fragile, fractured state of public trust in democratic institutions.









