Amazon Is Using Specialized AI Agents for Deep Bug Hunting
In an era defined by rapid technological advancement, the digital landscape is undergoing a profound transformation, spearheaded by the advent of generative artificial intelligence. While this innovative technology undeniably accelerates the pace of software development, it simultaneously amplifies the capabilities of digital attackers, empowering them to execute sophisticated, financially motivated, or state-backed hacks with unprecedented efficiency. This dual-edged sword presents a formidable challenge for security teams within major tech companies like Amazon, who are now confronted with an exponentially growing volume of code to review, all while facing escalating pressure from an increasingly sophisticated array of malicious actors. Recognizing this critical shift, Amazon is taking a pioneering step forward, publicly disclosing details of an internal system designed to tip the scales in favor of defense: Autonomous Threat Analysis (ATA). This groundbreaking system has been strategically deployed to empower Amazon’s security teams, enabling them to proactively pinpoint inherent weaknesses across its vast platforms, perform intricate variant analysis to swiftly uncover similar vulnerabilities, and subsequently engineer robust remediations and advanced detection capabilities, effectively plugging security holes before attackers can even discover them.
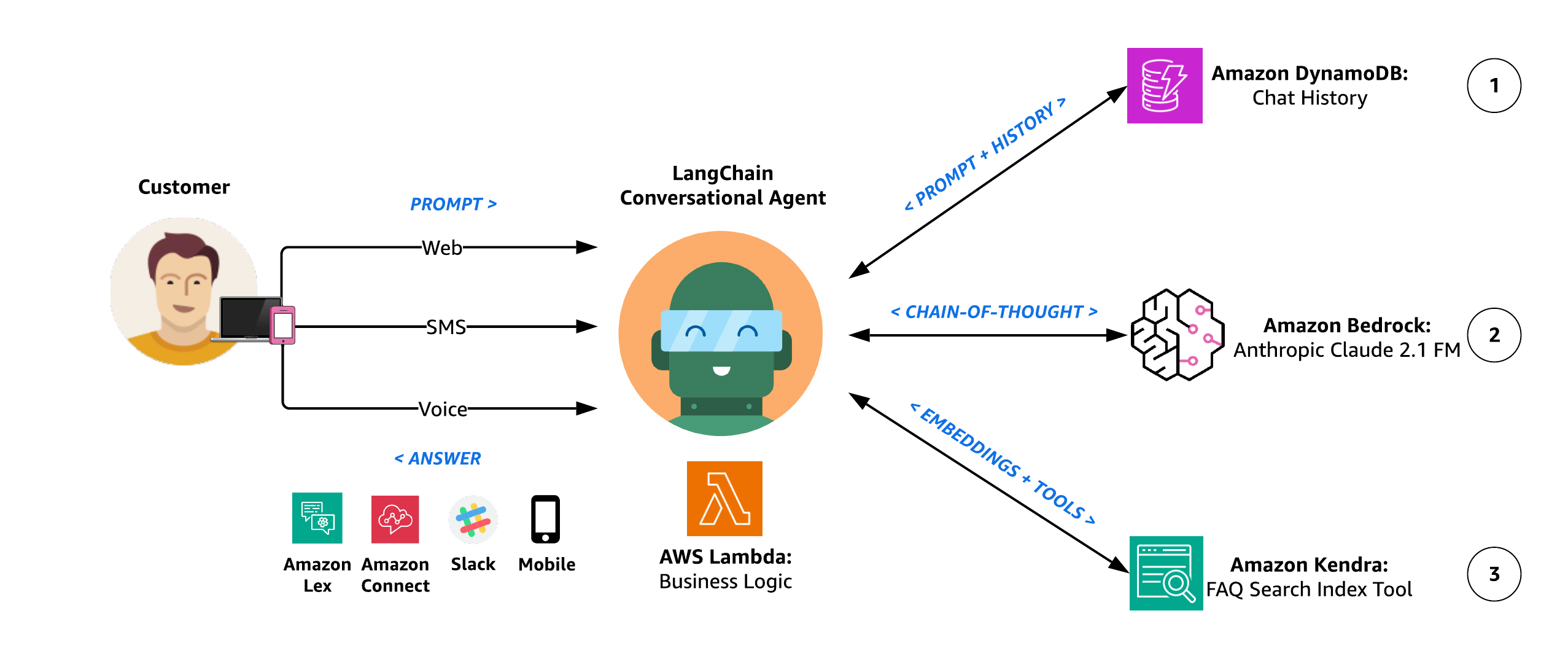
The genesis of ATA traces back to an internal Amazon hackathon held in August 2024, a testament to the company’s culture of innovation and problem-solving. What began as an experimental concept quickly evolved into an indispensable asset, a crucial tool that has significantly augmented Amazon’s security posture. The fundamental brilliance underpinning ATA lies not in its function as a monolithic, all-encompassing AI agent, but rather in its architectural elegance as a sophisticated ecosystem of multiple, specialized AI agents. These agents are designed to operate in a dynamic, competitive framework, organized into two opposing teams. This unique adversarial setup allows them to relentlessly investigate real-world attack techniques and meticulously explore various permutations of how these techniques could potentially be leveraged against Amazon’s intricate systems. Following their intensive analysis and simulated skirmishes, these specialized agents then propose highly refined security controls for subsequent human review, ensuring a critical layer of expert oversight.
Steve Schmidt, Amazon’s chief security officer, shed light on the imperative behind ATA’s creation, explaining to WIRED that the initial concept was conceived to directly address a critical limitation prevalent in traditional security testing methodologies: "limited coverage and the challenge of keeping detection capabilities current in a rapidly evolving threat landscape." He elaborated on the issue of "limited coverage," pointing out the inherent human constraint: "Limited coverage means you can’t get through all of the software or you can’t get to all of the applications because you just don’t have enough humans." This limitation is particularly acute for a company operating at Amazon’s scale, with an astronomical volume of code and a continuous deployment cycle. Furthermore, Schmidt emphasized the peril of static defenses: "And then it’s great to do an analysis of a set of software, but if you don’t keep the detection systems themselves up to date with the changes in the threat landscape, you’re missing half of the picture." ATA was engineered to overcome these twin challenges, offering a scalable, dynamic solution that transcends human limitations.
To facilitate the effective scaling and operation of ATA, Amazon invested significantly in developing bespoke "high-fidelity" testing environments. These environments are not merely simulations but are meticulously crafted, deeply realistic reflections of Amazon’s actual production systems. This critical design choice enables ATA to both ingest authentic operational telemetry and generate equally realistic data for analysis, ensuring that its findings are grounded in the true complexities and nuances of Amazon’s infrastructure. The accuracy and relevance of ATA’s work are paramount, and these specialized environments provide the perfect proving ground.
A cornerstone of ATA’s design philosophy is an unwavering commitment to verifiability. Amazon’s security teams meticulously engineered the system such that every technique it employs and every detection capability it produces is rigorously validated through real, automatic testing against live system data. This rigorous verification process is central to ATA’s reliability. For instance, the "red team" agents – those specifically tasked with identifying potential attacks against Amazon’s systems – execute actual commands within ATA’s specialized test environments. The outcomes of these commands are not theoretical; they generate verifiable logs, providing concrete evidence of their findings. Conversely, the "blue team" agents, focused on defense, leverage real telemetry to confirm the efficacy of the protections they propose. Anytime an agent, be it red or blue, develops a novel technique or proposes a new defense, it is mandated to pull time-stamped logs that unequivocally prove the accuracy and validity of its claims.
This stringent demand for observable evidence and verifiable outcomes dramatically reduces the incidence of false positives, a perennial headache for security teams. Schmidt aptly describes this built-in mechanism as "hallucination management." By architecturally mandating certain standards of empirical evidence, Schmidt confidently asserts that "hallucinations are architecturally impossible" within ATA’s operational framework. This proactive design choice addresses one of the most significant challenges in modern AI systems – ensuring trustworthiness and preventing erroneous outputs, particularly crucial in the high-stakes domain of cybersecurity. The system doesn’t merely suggest a vulnerability or a defense; it demonstrates it with concrete, reproducible data.
The very structure of ATA, where specialized agents collaborate in teams – each contributing its unique expertise towards a overarching security objective – mirrors the collaborative dynamics inherent in human security testing and defense development. However, the transformative power of AI, as articulated by Amazon security engineer Michael Moran, lies in its unparalleled capacity to rapidly generate novel variations and intricate combinations of offensive techniques, and subsequently propose equally innovative remediations, all at a scale that would be prohibitively time-consuming and resource-intensive for human teams alone. Moran, one of the engineers who originally championed ATA at the 2024 hackathon, enthusiastically notes, "I get to come in with all the novel techniques and say, ‘I wonder if this would work?’ And now I have an entire scaffolding and a lot of the base stuff is taken care of for me" in investigating it. He adds, "It makes my job way more fun but it also enables everything to run at machine speed." This synergy between human creativity and AI’s processing power allows for an unprecedented depth and breadth of security analysis.
Schmidt further highlights ATA’s demonstrable effectiveness in scrutinizing specific attack capabilities and rapidly generating highly effective defenses. In a compelling real-world example, the system was tasked with focusing on Python "reverse shell" techniques. A reverse shell is a critical hacker tool that manipulates a target device into initiating an outbound connection back to the attacker’s computer, effectively bypassing traditional firewall protections and granting remote control. Within a mere few hours, ATA not only uncovered a suite of new potential reverse shell tactics that human experts might have overlooked but also proposed corresponding detections for Amazon’s defense systems that, upon validation, proved to be 100 percent effective. This swift and precise identification and mitigation of a dangerous vulnerability underscore the system’s immense value.
While ATA executes its complex analytical tasks with remarkable autonomy, it operates firmly within a "human in the loop" methodology. This crucial design principle mandates that any proposed changes to Amazon’s core security systems must receive input and final approval from a real person before implementation. Schmidt readily acknowledges that ATA is not, nor is it intended to be, a wholesale replacement for the nuanced, sophisticated insights provided by advanced human security testing. Instead, he emphasizes its role as a force multiplier: for the massive quantity of mundane, repetitive, and time-consuming tasks inherent in daily threat analysis, ATA liberates human staff, granting them invaluable time to dedicate their expertise to tackling the most complex, strategic, and high-impact security challenges that require genuine human intuition and problem-solving.
Looking ahead, the next strategic phase for ATA, according to Schmidt, involves integrating it into real-time incident response protocols. This advancement promises even faster identification and remediation during actual cyberattacks on Amazon’s colossal and intricate systems, transforming reactive defense into a proactive, machine-speed response. The implications for minimizing damage and downtime are significant.
In conclusion, Schmidt encapsulates the profound positive impact of ATA: "AI does the grunt work behind the scenes. When our team is freed up from analyzing false positives, they can focus on real threats." He continues, "I think the part that’s most positive about this is the reception of our security engineers, because they see this as an opportunity where their talent is deployed where it matters most." ATA represents a paradigm shift in enterprise cybersecurity, leveraging the cutting edge of AI to not only enhance defensive capabilities at an unprecedented scale but also to fundamentally elevate the role of human security professionals, allowing them to channel their expertise into truly impactful work.









