Google lawsuit accuses China-based cybercriminals of massive text-message phishing scams.
In an unprecedented move poised to reshape the global fight against digital crime, Google has filed a federal lawsuit against a sophisticated network of foreign cybercriminals, primarily based in China, accused of orchestrating massive text-message phishing attacks. The tech giant, in an exclusive disclosure to CBS News, revealed that these malicious operations are part of a sprawling criminal enterprise dubbed "Lighthouse," which has reportedly compromised tens of millions of credit cards and impacted over a million victims within the United States alone. This landmark legal action, filed under the powerful RICO Act, signifies a strategic escalation by a major technology company against the burgeoning threat of "smishing" and aims to establish a critical legal precedent for combating organized cybercrime.
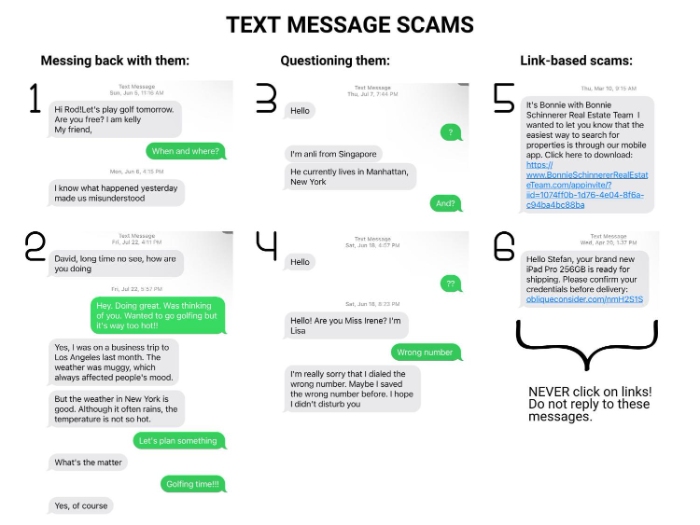
The attacks, characterized by their deceptive simplicity and widespread reach, leverage what is known as "smishing"—a portmanteau of SMS and phishing. Unlike traditional email phishing, smishing exploits the inherent trust many users place in text messages, often prompting immediate action. The messages crafted by the "Lighthouse" network are meticulously designed to appear legitimate, frequently employing urgent pretexts such as warnings about a "stuck package" delivery, an "unpaid toll," or other mundane but critical notifications. Recipients, often caught off guard, are then lured into clicking malicious links embedded within these texts. These links redirect them to fraudulent websites, often meticulously crafted to mimic legitimate services or companies, where they are prompted to divulge sensitive personal information, including passwords, banking details, and credit card numbers. Once harvested, this data becomes a commodity for further illicit activities, ranging from direct financial theft to identity fraud.
Halimah DeLaine Prado, Google’s General Counsel, articulated the severe scale of the threat posed by "Lighthouse." "These scammers ended up compromising anywhere from 15 million to 100 million potential credit cards within the U.S. and impacted, at our current estimates, over a million victims," she told CBS News. This staggering figure underscores the industrial scale and highly organized nature of the operation, pushing Google to pursue legal avenues typically reserved for dismantling traditional organized crime syndicates. The choice of the Racketeer Influenced and Corrupt Organizations (RICO) Act is particularly noteworthy. Enacted in 1970, RICO was originally designed to combat the Mafia and other criminal enterprises by targeting patterns of illegal activity rather than individual offenses. By invoking RICO, Google is asserting that "Lighthouse" operates as a cohesive, ongoing criminal organization, with its "phishing-as-a-service" platform serving as the infrastructure for a continuous pattern of racketeering activity.
The lawsuit specifically targets unknown operators, identified in the legal documents as "John Does 1 through 25," who are alleged to have built and maintained this sophisticated "phishing-as-a-service" platform. This model allows various cybercriminal affiliates to lease or subscribe to the platform’s tools and infrastructure, enabling them to launch mass text attacks without the need to develop their own sophisticated phishing kits. This "as-a-service" approach lowers the barrier to entry for aspiring criminals and significantly amplifies the reach and impact of their illicit activities, essentially democratizing cybercrime. Google’s complaint details how this network has exploited the company’s brand, creating over 100 fake websites that falsely display Google’s logo to enhance their credibility and trick users into surrendering their login credentials or credit card details. The sheer volume of compromised data highlights not only the network’s technical prowess but also its operational efficiency in exploiting human vulnerabilities.
DeLaine Prado clarified that the primary objective of this lawsuit is not necessarily to help individual victims recover their losses—a notoriously difficult task in cross-border cybercrime cases—but rather to serve as a powerful "deterrent for future criminals to create similar enterprises." This strategic focus underscores Google’s broader commitment to safeguarding its users and the digital ecosystem. By challenging these cybercriminals in a U.S. federal court under RICO, Google aims to send an unequivocal message that such activities will be met with robust legal action, potentially creating a new blueprint for how technology companies can legally confront and disrupt international cybercrime organizations. This move is less about immediate financial restitution and more about setting a foundational legal precedent, testing the applicability of a decades-old racketeering law to the complex, borderless landscape of 21st-century digital offenses.
The implications of such a lawsuit are far-reaching, as highlighted by cybersecurity expert Kevin Gosschalk, CEO of Arkose Labs. While acknowledging the inherent challenges in recovering funds lost to cybercriminals, Gosschalk emphasized the disruptive potential of Google’s action. "It has an impact on the ecosystem," he noted. "If there are three major players and you go after the big one and take it down, then the other two start second-guessing, ‘Hey, should we be in this business, or should we get out of this business?’" This "domino effect" could significantly destabilize the cybercrime market, making it riskier and less profitable for malicious actors. However, Gosschalk also pointed out the significant hurdles involved in pursuing cybercriminals operating in foreign jurisdictions, particularly in countries with limited extradition laws or weak legal enforcement mechanisms, such as Cambodia, where some of these operations are known to thrive. Despite these challenges, he affirmed that such legal actions do impose tangible consequences, stating, "it does mean the individuals behind those things will not be able to travel to the U.S. in the future, so it does add extra risk." This potential restriction on international travel for identified cybercriminals could serve as a powerful disincentive for those who value mobility and access to global resources.
For users, understanding and implementing robust cybersecurity practices remains the most effective defense against smishing and other forms of digital fraud. The core advice is simple yet critical: never click on links or reply to unknown or suspicious text messages. Instead, if a message purports to be from a legitimate entity (like a bank, delivery service, or government agency), independently verify its authenticity by contacting the organization directly through official channels (e.g., their official website or a customer service number found on their site, not from the text message itself).
Modern smartphones offer built-in features to help users combat these scams. iPhone users can enable "Filter Unknown Senders" and "Filter Junk" settings, which automatically sort messages from numbers not in their contacts into a separate folder. Similarly, Android users can enable "Spam Protection" within their messaging apps. Additionally, forwarding suspicious text messages to 7726 (SPAM) allows mobile carriers to investigate and block similar messages. It’s crucial, however, to periodically check these filtered folders, as legitimate messages from new contacts or services might occasionally be miscategorized. Beyond these filters, users are strongly advised to enable two-factor authentication (2FA) wherever possible, use strong and unique passwords for all online accounts, and be wary of any message that demands immediate action or asks for personal financial information.
Google’s lawsuit represents a significant escalation in the ongoing battle against global cybercrime. By leveraging the RICO Act against a sophisticated "phishing-as-a-service" enterprise, the company is not just seeking justice for past harms but is actively working to shape the legal landscape for future digital security. This move highlights the evolving role of tech giants in protecting their user base and infrastructure from increasingly organized and insidious threats. While the complexities of international jurisdiction and enforcement remain formidable, this landmark case could pave the way for more coordinated, aggressive legal strategies to dismantle criminal networks that operate beyond traditional borders, ultimately making the digital world a safer place for everyone. The outcome of this "first-of-its-kind" lawsuit will undoubtedly be closely watched by cybersecurity experts, legal scholars, and technology companies worldwide, as it could set a powerful precedent for holding international cybercriminals accountable under the weight of U.S. law.









